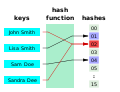
output. The values returned by a hash function are called hash values, hash codes, hash digests, digests, or simply hashes. The values are usually used to...
50 KB (7,536 words) - 16:10, 29 August 2024
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle...
48 KB (6,228 words) - 12:47, 4 September 2024
checksum. Hash function security summary Secure Hash Algorithms NIST hash function competition Key derivation functions (category) "Hash functions". www.azillionmonkeys...
10 KB (280 words) - 10:21, 23 June 2024
In computer science, a perfect hash function h for a set S is a hash function that maps distinct elements in S to a set of m integers, with no collisions...
24 KB (2,956 words) - 14:27, 22 July 2024
BLAKE is a cryptographic hash function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants...
30 KB (2,848 words) - 05:59, 18 August 2024
cryptography, Whirlpool (sometimes styled WHIRLPOOL) is a cryptographic hash function. It was designed by Vincent Rijmen (co-creator of the Advanced Encryption...
11 KB (1,054 words) - 03:57, 19 March 2024
The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S...
3 KB (464 words) - 13:15, 22 July 2024
hash function security/cryptanalysis can be found at hash function security summary. Basic general information about the cryptographic hash functions:...
16 KB (806 words) - 20:08, 6 August 2024
password, or a passphrase using a pseudorandom function (which typically uses a cryptographic hash function or block cipher). KDFs can be used to stretch...
13 KB (1,645 words) - 14:47, 4 August 2024
is a non-cryptographic hash function created by Glenn Fowler, Landon Curt Noll, and Kiem-Phong Vo. The basis of the FNV hash algorithm was taken from...
14 KB (1,342 words) - 15:52, 2 September 2024